In this post you will learn how to connect Android Debug Bridge (ADB) wirelessly via Wi-Fi instead of using a USB-cable. Assumptions Your Android-device has a Wi-Fi connection; Your workstation has a TCP/IP connection which is routable to the Android-device; Your Android-device is connected with your workstation using a USB-cable; ADB is installed on your… Continue reading Android: Use ADB wirelessly via Wi-Fi
Author: user
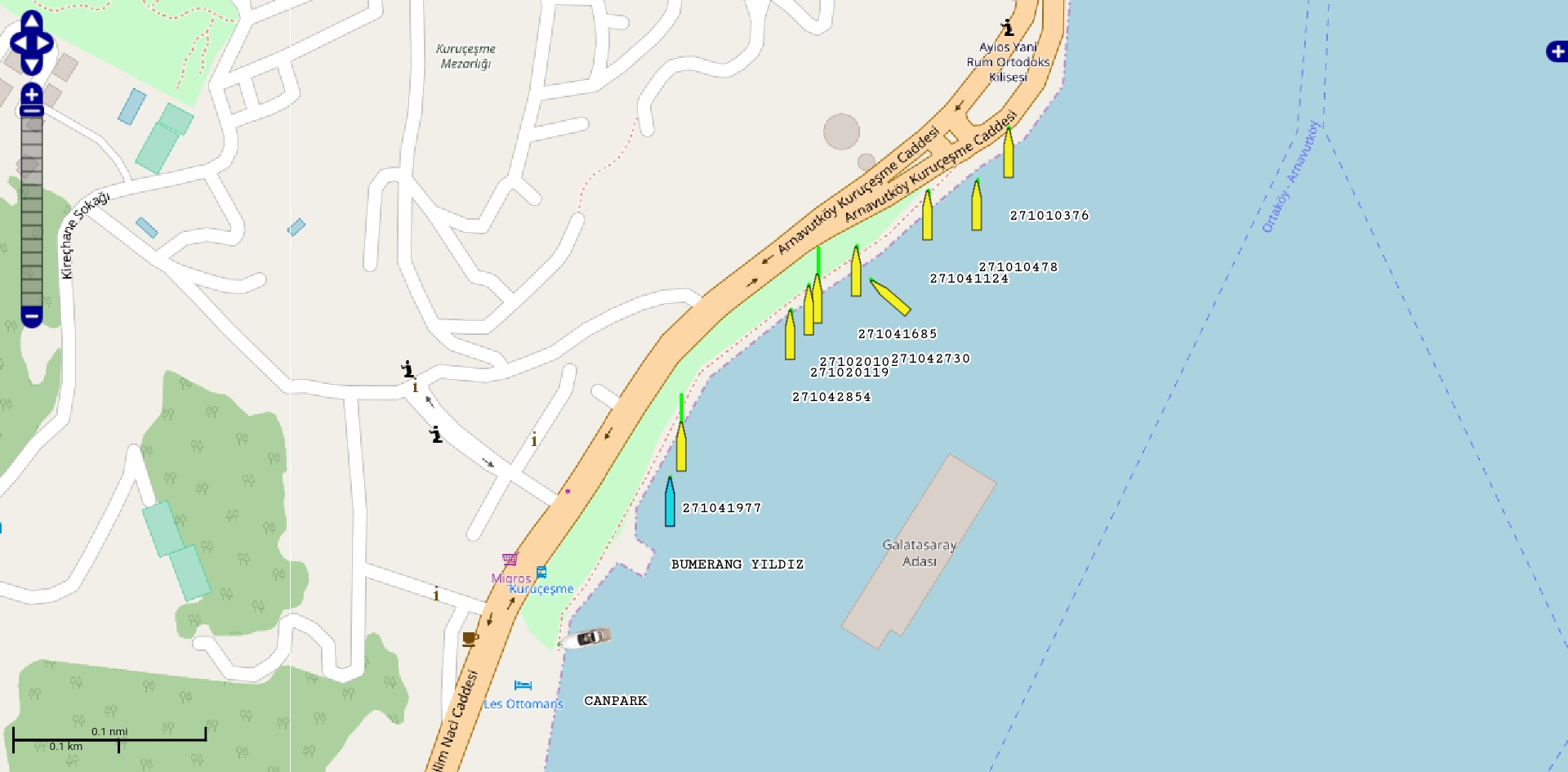
Ships – Android application
VIDEGRO’s Ships is a free Android application which allows you to receive AIS information directly from ships in your neighbourhood using a cheap DVB-T-DAB-FM / RTL-SDR receiver. IMPORTANT: You need to have an OTG capable Android device and a DVB-T-DAB-FM / RTL-SDR receiver, otherwise this application is useless. It is an all in one application.… Continue reading Ships – Android application
Public WiFi-hotspots and sensitive information, a good combination?
The holiday has been started, you love to check your e-mail, Facebook or WhatsApp at your holiday location but can you trust the provided Wi-Fi-connection? The answer is: NO. Never trust these kind of Wi-Fi-networks. Maybe somebody has set up a wireless access point (AP)/WLAN-hotspot with the same name as the access point of your… Continue reading Public WiFi-hotspots and sensitive information, a good combination?